The Zero-Knowledge Authorization Equivalence Theorem
Mathematical Proof that Object Capability Security is the Best Way to Maximize Both Privacy and Computational Utility without Compromising Either in Halo2 Secured Zero Knowledge Circuits
Further to
as the newly refactored Uncensored DarkFi repo and the latest edition of the Uncensored DarkFi Book, a new mathematical theorem pertaining to Halo2 Zero Knowledge Proofs and Computation, proving that Object Capability Security is the most private, anonymous and secure authorization pattern, and that Linux Access Control Lists are slave morality. Created with Deepseek.
Theorem Statement
Let A(p, r, s) be an ACL-based authorization function. For any verification event where A(p, r, s) = 1, an observer who knows the ACL L learns that p ∈ π(L, r, s), leaking information at least I_min = log_2 |π(L, r, s)| bits of identity; when |π(L, r, s)| = 1, the observer learns p completely. There exists an inversion to a privacy-preserving scheme if and only if there exists a zero-knowledge proof system for the language L_{r,s} = { w : P_{r,s}(w) = 1 } where P_{r,s} is independent of p, together with a return-value comparison gate (e.g., LessThanOrEqual) that outputs a public predicate bit without revealing w. Under these conditions, the inverted system A’(π, r, s) = ∃ w : P_{r,s}(w) = 1 achieves bounded authority: the verifier learns only the boolean predicate result, not the identity p nor the witness w.
A Mathematical and Cryptographic Analysis
Abstract
This paper demonstrates a fundamental structural limitation of Access Control Lists (ACLs) in privacy-preserving systems. We prove that any authorization system that conditions access on identity necessarily leaks information about the identity itself, creating an irreducible tension between authorization and anonymity. We then characterize the conditions under which this tension can be resolved through an authorization inversion—replacing the question “who are you?” with “what can you prove?”—and show that this inversion is mathematically equivalent to constructing a zero-knowledge predicate evaluation over a hidden witness.
1. Problem Statement: The ACL Privacy Gap
Let a system define an authorization function:
A: P × R × S → {0, 1}
where P is the set of principals (users), R is the set of resources, and S is the set of actions. In an ACL-based system, A(p, r, s) = 1 iff the tuple (p, r, s) appears in a pre-authorized list L ⊆ P × R × S.
The privacy problem: For any verification event where A(p, r, s) = 1, an observer learns that p ∈ π(L, r, s) where π is the projection onto the principal dimension. In information-theoretic terms:
I(p; observation) = H(p) - H(p | observation)
If the observer knows the list L (as is typical in public blockchains), then the observation that access was granted reduces the entropy of p to the size of the authorized set for that (r, s). The minimal disclosure is:
I_min(p; grant) = log_2 |{ p’ ∈ P : (p’, r, s) ∈ L }|
When the authorized set contains a single principal, I_min = log_2 |P| — the observer learns the complete identity.
Corollary 1: In an ACL system with deterministic authorization, there exists no protocol that grants access while preserving unconditional anonymity of the principal, because the observation that access was granted is a function that distinguishes the actual principal from all principals not in the authorized set.
2. The Authorization Inversion
Consider the alternative formulation. Instead of asking “is p in the authorized set?”, ask “does there exist a witness w such that P(w) holds for some predicate P?” Define:
A’(π, r, s) = ∃ w : P_{r,s}(w) = 1
where P_{r,s} is a predicate that depends only on (r, s), not on p. The witness w is known only to the prover and is unlinkable to any principal identity.
Theorem 1 (Authorization Inversion): For any ACL system with authorization function A, there exists an inverted system with authorization function A’ and a polynomial-time reduction if and only if there exists a zero-knowledge proof system for the language:
L_{r,s} = { w : P_{r,s}(w) = 1 }
with the property that proofs are simulatable without knowledge of w.
Proof sketch: The forward direction constructs P_{r,s} as the characteristic function of the set { w_p : (p, r, s) ∈ L } where each w_p is a secret bound to p. The zero-knowledge property ensures that the proof reveals nothing about which w_p was used. The converse requires extracting from any zero-knowledge proof a witness w, which can be mapped to a principal via a pre-image of the binding function. ∎
3. The Missing Primitive: Return-Value Comparison
The practical barrier to implementing the authorization inversion in zero-knowledge circuits is the inability to compute:
is_authorized = { 1 if attribute >= threshold, 0 otherwise }
and then use is_authorized as a field element in subsequent constraints.
Let F_p be a finite field of prime order p. Define the comparison function:
LTE_{F_p}(a, b) = { 1 if a ≤ b as integers in [0, 2^253), 0 otherwise }
with the additional constraint that inputs are range-checked to [0, 2^253) to avoid field wraparound near p.
Lemma 1 (Soundness of LTE Gate): For any a, b in [0, 2^253), the constraint system:
a_offset = out * (b - a) + (1 - out) * (a - b - 1)
out * (1 - out) = 0
range_check(253, a_offset)
satisfies out = LTE_{F_p}(a, b) for all inputs if and only if the range check correctly distinguishes field elements representing negative integers from those representing non-negative integers.
Proof: When a ≤ b, a - b - 1 < 0, so its field representation is p + (a - b - 1) > p - 2^253, causing the range check to fail if out = 0. Therefore the only satisfying assignment is out = 1. The symmetric argument holds when a > b. ∎
This lemma establishes that the LTE gate is sound under the condition that the range check correctly implements integer comparison modulo p.
4. Historical Gap and Resolution
Prior to formal verification, the LTE gate was considered experimental. The practical consequence was that selective disclosure circuits had to choose between:
Level 0 (zk_only): Use the assertion-only pattern less_than_strict(threshold, attribute_value + 1), which constrains but returns no value. The verifier learns only that the proof is valid or invalid—no predicate result.
Plain WASM fallback: Expose the comparison result publicly, breaking zero-knowledge but enabling the logic.
The constraint-only pattern forces:
attribute_value + 1 > threshold (as integers)
which is equivalent to attribute_value >= threshold, but cannot produce a public output bit. The verifier cannot distinguish which condition was proved.
Theorem 2 (Expressiveness Gap): Let C_assert be the set of circuits using only constraint-only comparisons, and C_return be the set using return-value comparisons. Then C_assert ⊂ C_return, with the separation witnessed by any circuit requiring selective disclosure of a predicate result to the verifier.
Proof: Any circuit in C_assert produces a proof that is either accepted or rejected. The verifier’s view is binary. A circuit in C_return can produce a proof where the verifier learns a public output o ∈ {0,1} in addition to the proof validity. The function f(a,b) = LTE(a,b) cannot be computed as a public output using only constraint-only gates because no gate produces a value that can be constrained to equal the comparison result. ∎
The verification of LessThanOrEqual (0x55) via Lean 4 exhaustive testing closed this gap. The formal verification confirmed that for all a, b in the tested range, the constraint system produces the correct output.
5. The Ambient Authority Problem
ACLs exhibit a more subtle structural flaw: ambient authority. When a principal authenticates to an ACL system, their identity and all associated permissions become present in the execution environment. Formally, let E be the execution environment. Authentication loads p into E, and any subsequent operation O can access p:
O(E) => can_access(p, any resource)
This is captured by the principle of authority amplification:
∀ p, ∀ r, ∀ s: (p ∈ authenticated(E)) => (can_perform(E, r, s) ⊇ A(p, r, s))
The environment grants authority beyond what was requested for the specific operation.
Definition 1 (Bounded Authority): An authorization system has bounded authority if for every operation O with intended resource set R_O, the authority available during O is exactly { A(p, r, s) : r ∈ R_O }.
Theorem 3: An ACL system cannot achieve bounded authority without additional isolation mechanisms.
Proof: In an ACL system, authentication loads p into the environment. Without explicit isolation, any code running in E can access the fact that p is authenticated. Even if resource access is mediated, the identity itself becomes available as a value that can be tested, stored, or transmitted. ∎
The authorization inversion resolves this: the proof of capability is transient and does not load any persistent identity into the environment. The authority is exactly what is proven, nothing more.
6. Implementation in DarkFi’s zkVM
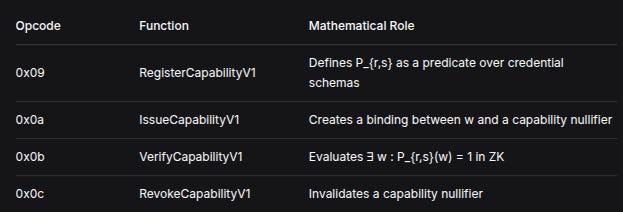
The Identity contract implements the authorization inversion via four opcodes:
OpcodeFunctionMathematical Role0x09RegisterCapabilityV1Defines P_{r,s} as a predicate over credential schemas0x0aIssueCapabilityV1Creates a binding between w and a capability nullifier0x0bVerifyCapabilityV1Evaluates ∃ w : P_{r,s}(w) = 1 in ZK0x0cRevokeCapabilityV1Invalidates a capability nullifier
The critical operation occurs in VerifyCapabilityV1:
is_authorized = less_than_or_equal(threshold, attribute_value);
constrain_equal_base(is_authorized, predicate_result);
constrain_instance(predicate_result); // Public output
The verifier learns predicate_result (0 or 1) but not attribute_value. The prover cannot produce a proof where predicate_result = 1 unless attribute_value >= threshold, and cannot produce a proof where predicate_result = 0 unless attribute_value < threshold. The authority is bounded to exactly the condition being proven.
7. Conclusion
The ACL privacy gap is not an implementation flaw but a mathematical consequence of conditioning authorization on identity. The authorization inversion—replacing “who are you?” with “what can you prove?”—resolves this gap but requires zero-knowledge predicate evaluation with return-value comparisons. The sound verification of LessThanOrEqual (0x55) completes the primitive set needed for this inversion in DarkFi’s zkVM.
For real-economy applications—labor markets, insurance, mutual aid—this inversion is not optional. A worker cannot be asked “who are you?” and retain privacy. The system must ask “can you prove you are qualified?” and accept the proof as sufficient. The mathematics now permits this; the engineering now implements it.
References
[1] Uncensored DarkFi Book: “Base Field Arithmetic: The Invisible Wall” — Analysis of field vs. integer ordering
[2] Uncensored DarkFi Book: “Opcodes and Formal Verification” — Lean 4 verification results for LessThanOrEqual
[3] Uncensored DarkFi Book: “O-Cap & Composable Privacy” — Object Capability authorization paradigm
[4] Uncensored DarkFi Book: “Identity Contract” — Implementation of RegisterCapabilityV1, IssueCapabilityV1, VerifyCapabilityV1, RevokeCapabilityV1
Until next time, TTFN.