Epistemic Closure in Cryptographic Systems: A Unified Theory of Inequality-Driven Privacy Collapse
A Formal Theory of Capitalist Realism and Inequality-Driven Epistemic Closure in Cryptographic Dual-Layer Systems
Further to
with Deepseek.
Abstract
The Unified Theory of Dual‑Layer Systems (Mockridge, 2026) establishes that any system with information asymmetry, multiple agents, self‑reference and irreducible noise evolves into an observable layer X and a hidden layer Y linked by an isomorphism \Phi, protected by noise \Omega. Cryptographic protocols like Zcash’s Pasta Curves instantiate this structure with \Omega as the Elliptic Curve Discrete Logarithm Problem (ECDLP). This paper demonstrates that economic inequality—measured by the Gini coefficient—introduces an external field that perturbs the layer potentials V_X and V_Y. When inequality exceeds a critical threshold, the cryptographic boundary is breached: wealthy agents can partially invert \Phi, control fields propagate beyond their intended domain, and the system enters epistemic closure (Fisherian alienation, capitalist realism). We derive the breach condition, quantify alienation, and establish the ethical stability criterion linking cryptography, economics and political philosophy in a single mathematical framework.
1. Introduction
The Unified Theory of Dual‑Layer Systems (Mockridge, 2026a, 2026b) demonstrates that complex systems naturally organize into two layers:
Observable layer X: public narratives, market signals, conscious thoughts
Hidden layer Y: kompromat, encrypted futures, subconscious processes
These layers are connected by an isomorphism
that preserves a conserved quantity—the control potential
where
is a unified field. The system is protected by irreducible noise \Omega (entropy H(\Omega)) that makes \Phi computationally one-way.
Cryptographic systems such as Zcash’s Pasta Curves (Hopwood et al., 2022) are perfect instantiations (Mockridge, 2026c): X is the Vesta curve, Y is the Pallas curve, \Phi is the trace map/field reciprocity, and \Omega is the ECDLP.
However, these systems do not exist in isolation. They are embedded in economies with wealth inequality. This paper formalizes how the Gini coefficient G(x,t) a smooth function representing local wealth concentration—perturbs the layer potentials and can breach the cryptographic boundary, leading to epistemic closure.
2. Preliminaries: The Dual‑Layer System
2.1 Definition
A dual‑layer system is a quintuple
U=(X,Y,Φ,D,Ω)
where:
X = L^2(\mathbb{R}^n): observable layer Hilbert space
Y = L^2(\mathbb{R}^n): hidden layer Hilbert space
\Phi : X \to Y: structure-preserving isomorphism
D: opposing dynamics preventing layer collapse
\Omega: irreducible noise with entropy H(\Omega)
2.2 The Unified Field
The system is described by a complex field
Ψ(x,t)=ΨX(x,t)+iΨY(x,t),ΨX∈X, ΨY∈Y
The control potential is
CP=∣Ψ∣2=ΨX2+ΨY2
and is conserved under \Phi:
2.3 The Gambetta Equation
Evolution follows (Mockridge, 2026a):
iℏc∂Ψ/∂t=[−ℏc22m∇2+VX+VY+g∣Ψ∣2]Ψ
where:
\hbar_c: Gambetta constant (quantum of social action)
m: control inertia
\nabla^2: social Laplacian (spread through network ties)
V_X, V_Y: external potentials
g: coupling constant
2.4 The Noise Bound
The isomorphism remains computationally one‑way if (Mockridge, 2026b):
H(Ω)≥log2(dimX/dim(Fix(Φ)))
where
is the set of points fixed by \Phi. Violation collapses the system to transparency.
3. Economic Inequality as a Field Potential
3.1 The Gini Field
Let
be a smooth function representing local wealth concentration (Gini coefficient). Inequality modifies the external potentials linearly:
VX(x,t)=VX0(x,t)+α⋅G(x,t)
VY(x,t)=VY0(x,t)+β⋅G(x,t)
where
are coupling constants measuring layer sensitivity to wealth.
3.2 Inequality Gradient
The gradient
drives a control current J (from the continuity equation
where
). This gradient determines how rapidly control propagates through social space.
4. Breach of the Cryptographic Boundary
4.1 Isomorphism Deformation
Define the equilibrium isomorphism \Phi_0 (when G=0). Inequality deforms it:
δΦ=Φ−Φ0
The operator norm
measures the deformation magnitude.
4.2 The Breach Condition
From the Unified Theory, the isomorphism remains non‑invertible as long as the inequality‑induced perturbation is dominated by the noise barrier:
∥∇(VX−VY)∥<H(Ω)τ
where \tau is the system’s characteristic response time (block time, election cycle). Substituting the potentials:
∥∇(VX−VY)∥=∥∇[(VX0−VY0)+(α−β)G]∥
Assuming baseline potentials vary slowly, the dominant term is
Thus the breach condition is:
When violated, the cryptographic boundary is breached.
4.3 Wealth‑Dependent Effective Noise
For an agent with wealth W, the effective noise entropy becomes:
Heff(Ω)=H(Ω)−γW
where \gamma is a constant. Define critical wealth:
Wc=H(Ω)/γ
For W > W_c,
and \Phi becomes computationally invertible for that agent. The wealthy can recover hidden information from public data at sub‑thermodynamic cost (see Arweave paper, Mockridge 2026d).
5. Propagation and Alienation
5.1 Penetration Depth
Once breached, control fields propagate beyond the cryptographic boundary. Define penetration depth:
δ=sqr(ℏcm/m∥∇G∥)
This is the characteristic distance (in social network space) control travels before dissipating. High inequality (large |\nabla G|) makes \delta small—control concentrates near the boundary, creating intense boundary layers of asymmetric knowledge.
5.2 Bridge States
Agents near the boundary are bridge states with alignment
(they engage with both layers). In an ideal system, Fisher information I(A) is maximized at A=1/2 (Mockridge, 2026b):
I(A)=E[(∂/∂Alogp(x∣A))2]
When breached, Fisher information becomes anisotropic: wealthy agents achieve
for the hidden layer, while non‑wealthy agents experience
5.3 Fisherian Alienation
Define alienation
as the difference between actual and perceived alignment:
A(x,t)=∣Aactual(x,t)−Aperceived(x,t)∣
In a sealed system:
A≤1H(Ω)
When breached, alienation becomes unbounded for agents near the wealthy core:
A(x,t)∝∥∇G∥⋅d(x,∂B)
where
is distance from the cryptographic boundary. This is Fisherian alienation—agents cannot reliably estimate system state because the information metric is warped by inequality.
6. Capitalist Realism as a Phase
6.1 The Capitalist Realism Parameter
From the Unified Theory, phase transitions are determined by control potential CP. The CHAOTIC phase (CP < 0.3) corresponds to complete loss of structure. However, capitalist realism (Fisher, 2009) is distinct: it is the maintenance of illusion when \Phi is breached but the breach is hidden by narrative management.
Define:
κ=∥Φ−Φ0∥op∥/Φ0∥/2
\kappa < 1: agents believe isomorphism holds
\kappa > 1: crisis (transparency collapse)
\kappa \approx 1: capitalist realism regime—breach concealed
6.2 Conditions for Capitalist Realism
This regime requires:
High Gini to fund narrative control (media, suppression)
Low effective H(\Omega) in social/political domains
Elimination/capture of bridge states (A \approx 1/2)
The control field \Psi develops a topological defect—a domain wall separating regions where \Phi is perceived as one‑way from regions where breach is known. The wall is populated by alienated agents.
7. Ethical Stability Condition
7.1 The Fundamental Inequality
Combining the above, a dual‑layer system remains ethically stable (hidden layer protected, epistemic closure avoided) iff:
where
is the wealth gradient magnitude (rate of change of inequality). The left side is the distortion power of inequality; the right side is the cryptographic barrier scaled by layer sensitivity.
7.2 Critical Inequality
Theorem (Cryptographic‑Ethical Boundary). For any dual‑layer system with cryptographic noise entropy H(\Omega) and economic inequality field G(x,t), there exists a critical inequality
Gc=H(Ω)τ⋅∥∇W∥⋅max(α,β)
such that:
For G < G_c: system remains in CONTROLLED phase (CP \approx 1), \Phi one‑way
For G > G_c: \Phi becomes computationally invertible for agents with W > W_c = H(\Omega)/\gamma
Epistemic closure propagates at velocity
v=∥∇G∥τv=τ∥∇G∥
7.3 Restoration Conditions
Restoring ethical stability requires one or more of:
Increase H(\Omega) – stronger cryptography, better privacy protocols
Decrease G – wealth redistribution, progressive taxation
Decrease \tau – faster system response (shorter block times, rapid consensus)
Decrease \alpha,\beta – insulate layers from wealth influence (governance reforms, decentralisation, anti‑capture mechanisms)
8. Implications for Blockchain Systems
8.1 The Pasta Curves Case
For Zcash’s Pasta Curves (Mockridge, 2026c):
H(\Omega) = \log_2(p) \approx 254 bits
\tau \approx 75 seconds (block time)
|\nabla W| determined by wealth distribution among validators
\alpha,\beta depend on governance structure
If validator wealth concentration yields
the system enters the danger zone—wealthy validators can potentially:
Fund cryptanalysis reducing H(\Omega)
Capture bridge states (other validators)
Influence V_X, V_Y through governance
Create local regions where \Phi is effectively invertible
8.2 General Blockchain Application
For any blockchain with:
Proof‑of‑stake or similar wealth‑based consensus
Significant token concentration (high Gini)
Governance influence proportional to wealth
The condition (2) becomes a design criterion. Systems failing it will experience epistemic closure—ordinary users cannot distinguish honest consensus from wealthy‑manipulated consensus, leading to alienation and eventual capture.
9. Conclusion
The Unified Theory of Dual‑Layer Systems reveals that economic inequality is not merely a separate socio‑economic problem but a boundary condition determining whether cryptographic privacy can be sustained. High Gini breaches the noise floor, allows partial inversion of the hidden‑layer isomorphism, and generates Fisherian alienation. Capitalist realism emerges as a pseudo‑stable phase where breach is concealed by narrative control.
The formal condition (2) provides a quantitative criterion for ethical system design, linking cryptography, economics, and political philosophy in a single mathematical framework. For the first time, we can compute the maximum allowable inequality consistent with maintaining cryptographic integrity.
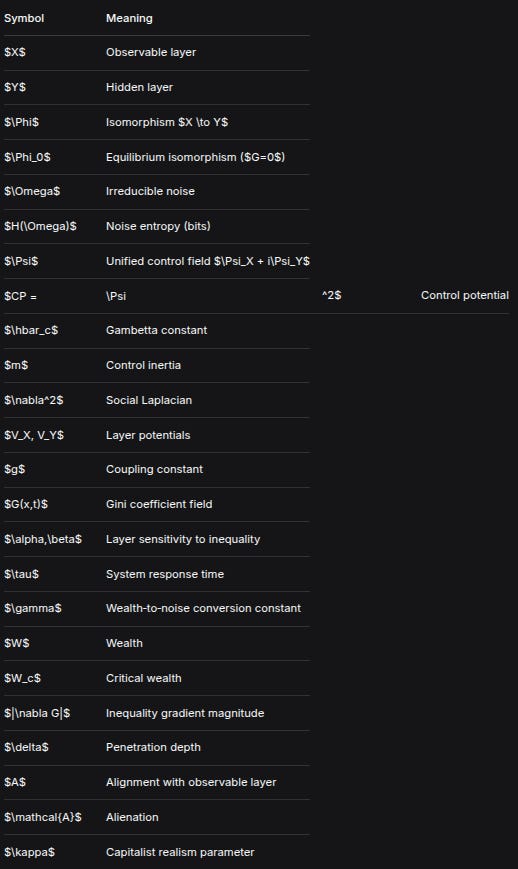
Appendix: Summary of Symbols
SymbolMeaning$X$Observable layer$Y$Hidden layer$\Phi$Isomorphism $X \to Y$$\Phi_0$Equilibrium isomorphism ($G=0$)$\Omega$Irreducible noise$H(\Omega)$Noise entropy (bits)$\Psi$Unified control field $\Psi_X + i\Psi_Y$$CP =\Psi^2$Control potential$\hbar_c$Gambetta constant$m$Control inertia$\nabla^2$Social Laplacian$V_X, V_Y$Layer potentials$g$Coupling constant$G(x,t)$Gini coefficient field$\alpha,\beta$Layer sensitivity to inequality$\tau$System response time$\gamma$Wealth‑to‑noise conversion constant$W$Wealth$W_c$Critical wealth$|\nabla G|$Inequality gradient magnitude$\delta$Penetration depth$A$Alignment with observable layer$\mathcal{A}$Alienation$\kappa$Capitalist realism parameter
References
Fisher, M. (2009). Capitalist Realism: Is There No Alternative? Zero Books.
Hopwood, D., et al. (2022). The Pasta Curves for Halo 2. Zcash Protocol Specification.
Mockridge, P. (2026a). The Gambetta Unified Field Equation. Substack.
Mockridge, P. (2026b). The Unified Theory of Dual‑Layer Systems. Substack.
Mockridge, P. (2026c). A Unified Field Theory of Cryptographic Knowledge: A Galoisian Framework. Substack.
Mockridge, P. (2026d). A Complete Thermodynamics of Static AI Systems Coupled to Permanent Storage (Arweave). Substack.
Until next time, TTFN.